What is the MITRE Insider Threat Framework Initiative?
MITRE is creating an evolving, data-driven Insider Threat Framework that includes psycho-social and cyber-physical characteristics as common and observable indicators for insider risks. MITRE’s framework will help Insider Threat/Risk Programs more accurately target and operationalize their deterrence, detection, and mitigation of insider threats. Existing frameworks of insider threats ignore psycho-social characteristics, focus solely on cyber, and/or are based on minimal or poor quality data.
How will the Framework be created?
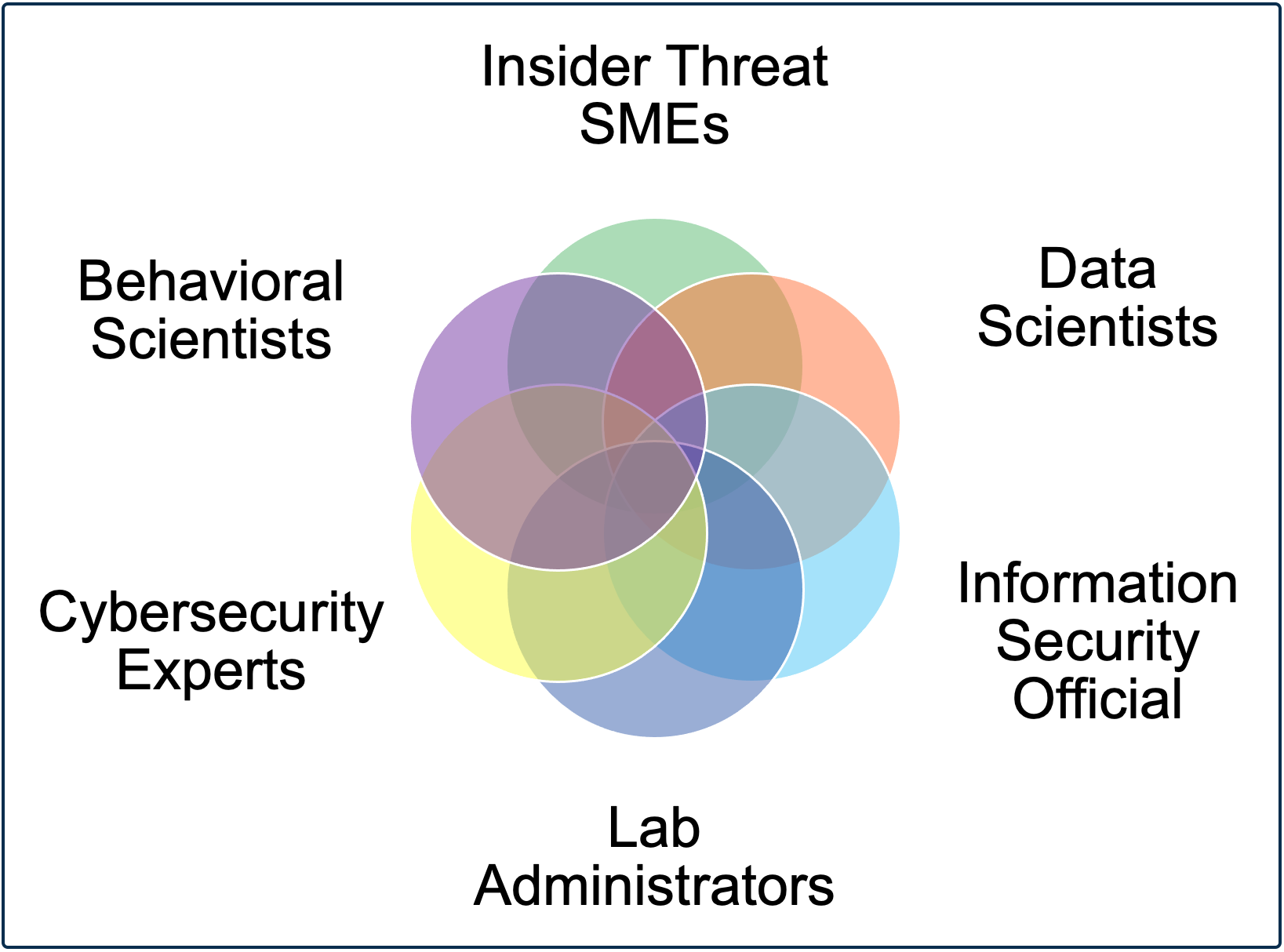
MITRE receives raw insider threat case data from government and industry organizations. Sensitive insider threat data is received, stored, processed, and analyzed in an access-controlled, closed-network MITRE Insider Threat Lab, where a team of behavioral scientists, insider threat subject matter experts, data scientists, and cyber security engineers consistently aggregate, structure, hand-code, and analyze the data.
The team will identify nation-level and sector-level patterns and trends. The framework–but not the raw or aggregated data–will be discreetly shared with vetted insider threat community leaders on a need-to-know basis (i.e., the framework will not be publicly accessible). MITRE plans to transition the findings via no-cost licensing to make our nation and the world a safer place.
Has this work already been done?
There is currently no data-driven comprehensive threat framework for insider threat. While there have been some attempts to develop conceptual threat frameworks for insider threat, those efforts are generally based on theory or have limited or no utility due to inadequate data quantity and quality. Most existing frameworks fail to account for both behavioral and cyber aspects of insider threat.
Threat frameworks for external adversaries do not work for insider threat. Insider threats simply act differently than Advanced Persistent Threats (APTs). Malicious insiders know how to leverage organizational processes to meet their objectives, they obfuscate malicious activities inside their legitimate work activity, and they take actions that do not require them to directly interact with cyber systems or break rules. Malicious insiders engage in more than just cyber activities, and any credible, effective insider threat framework must account for the cyber, physical, organizational, and human components of insider threat.
Why do we need a Framework?
Once completed, the MITRE Insider Threat Framework will help government and industry organizations improve their insider threat capabilities and use evidence in the following ways:
-
- Data-driven design: Design, target, and deploy deterrence, detection, and mitigation efforts based on evidence
- Prune your program: Discard or modify efforts that are found ineffective or even counterproductive
- Secure support: Use evidence to build support more effectively from key organizational stakeholders and data/resource owners (e.g., legal, human resources, security)
- Understand your adversary: Identify patterns and changes in behavior to detect malicious insider risks more proactively
- Verification: Verify deterrence, detection and mitigation processes work as expected
- Informed risk-taking: Assess whether program design decisions are appropriate
- Focus and assess vendors: Proactively drive the commercial vendor marketplace and better assess what you need and if a given vendor fulfils that need
What are the benefits of contributing data?
Your organization has the opportunity to contribute to the cutting-edge of insider threat science and practice. Sharing case data will accelerate the development of the framework and benefit your organization in the following ways:
- Representation: Improve the applicability of the framework structure and findings to your organization
- Engage expertise: Early access to the evolving framework and the insight and experience of MITRE’s behavioral sciences and insider threat subject matter experts
Community of interest: Engage with – and learn from – Insider Risk/Threat Programs across your and other sectors - Proactive responsibility: Insider threat is not just a corporate problem – it’s a national responsibility. Your organization can demonstrate leadership in this critical field
What do I need to do to contribute data or funding to the Framework?
For organizations interested in contributing data to the Insider Threat Framework Initiative, MITRE will work with you to secure approvals within your organization. We are experienced in briefing the importance of the framework initiative and the security of our lab to C-suite executives and governance boards who understandably must approve sharing sensitive organization data, including data protections, return on investment, and setting clear expectations about the types of data needed for success.
As to the amount of data required to participate, any number of cases is valuable. There is no such thing as “not enough data” to contribute. For example, some organizations have sent 5 cases and others provide fifty or hundreds of cases. We only ask that cases be closed, rather than in-progress to preserve the integrity of any ongoing investigation process for your organization and your employees.
We will work with you to transfer the data securely. Very minimal preparation of the data is required, as our air-gapped MITRE Insider Threat Lab is designed to handle and aggregate data from a variety of different formats.
Why is MITRE doing this?
MITRE is a trusted curator and convener of sensitive data with the necessary know-how and subject-matter expertise to successfully develop an Insider Threat Framework. As a not-for-profit organization, we play an objective, independent role in public-private partnerships. We already have trusted access to sensitive insider threat data from partners who know that we have appropriate controls and oversight in place. Our multi-disciplinary team is comprised of nationally and internationally recognized subject-matter-experts with over fifteen years of research and practice in insider threat programs and backgrounds across the behavioral sciences, data sciences, and cybersecurity. We have demonstrated experience with other public-private data-sharing initiatives, such as ASIAS (Aviation Safety Information Sharing and Analysis), a program that fuses government and industry data sources to proactively identify safety trends and assess the impact of changes in the aviation operating environment.
MITRE Insider Threat Lab
What is the MITRE Insider Threat Lab (InT Lab) – and what does it do?
MITRE is trusted curator of highly sensitive industry and government insider threat data. Organizations voluntarily contribute their insider threat case data for analysis by the MITRE Insider Threat Capability in the MITRE Insider Threat Lab located in McLean, Virginia (USA). The InT Lab is a secure and air-gapped MITRE facility built for curating and extracting value from sensitive insider threat data shared from the insider threat community in government and critical infrastructure industry both nationally and internationally. Since 2017, the multidisciplinary team has used the InT Lab to receive, store, process, clean, structure, analyze, collate, and interpret sensitive insider threat data from across cyber, physical, human, and organizational data sources. The InT Lab and the data within are protected by stringent physical security, information security, personnel security, and contractual safeguards including being NIST 800-171 compliant.
The InT Lab team has extensive experience conducting scientific research into insider threats, working in/with insider threat programs, and conducting the analysis of human-generated cyber and non-cyber data.
The air-gapped InT Lab handles insider threat case data from cyber and non-cyber sources including case management systems (e.g., investigative case notes), endpoint sensors (e.g., User Activity Monitoring Tools), and network and perimeter sensors (e.g., web proxy, data loss prevention tools). The InT Lab is equipped with workstations and application, file, and database servers furnished with tools to:
-
- Convert, collate, restructure and process data
- Extract the metadata
- Parse out user-generated vs. system-generated activities in cyber log files
- Automatically tag and categorize activities, flags, and other context from different cyber and non-cyber data sources
- Annotate by hand the case files where automated structuring is not appropriate or feasible
- Conduct advanced quantitative analyses (e.g., time-series analyses, multi-level modelling, random forests and other classification techniques, cluster analyses)
- Identify patterns of malicious activity by collating data across different cases
- Compare patterns of malicious activity to organizational baselines to reduce false positive rates
- Test and evaluate most promising potential risk indicators
MITRE Insider Threat Lab Team Skillsets and Experience
MITRE Insider Threat Lab Tools
- Data transfer, decompression, decryption, and backup: AWS Snowball, WinZip
- Data conversion, processing and structuring: Python, Perl, R
- Quantitative data analysis: R, SPSS, Tableau
- Qualitative hand-annotate software: Atlas.ti, Nvivo, Standard productivity tools
- IDEs: Anaconda, Notepad++, PyCharm, rStudio, Jupyter Notebooks, Visual Studio
- Offline mirror of Python, Perl and R libraries: Conversion, parsing, string and language processing, mining, structuring, manipulation, filtering, reformatting, statistics, and visualization
-
- Identify a large collection of novel, non-obvious remote cyber indicators of concerning search, collection, and removal of data from a live production network
- Develop unique combinations or clusters of remote-worker cyber indicators to detect malicious insider risk, with exceedingly low false positive and miss rates when compared to current ‘single indicator’ approaches used by Insider Threat/Risk Programs
- Conduct the first exploration of malicious insiders’ exfiltration patterns as well as identifying unique, creative threat vectors for data exfiltration by malicious insiders – and how these differ from employees sending data off-network as part of job
- Counter pervasive myths about insider threat using data to bust myths that Tactics, Techniques, and Procedures (TTPs) from APT frameworks and common methods of anomaly detection are useful for insider threat