Our Approach
MITRE’s Human-Focused Insider Threat Types
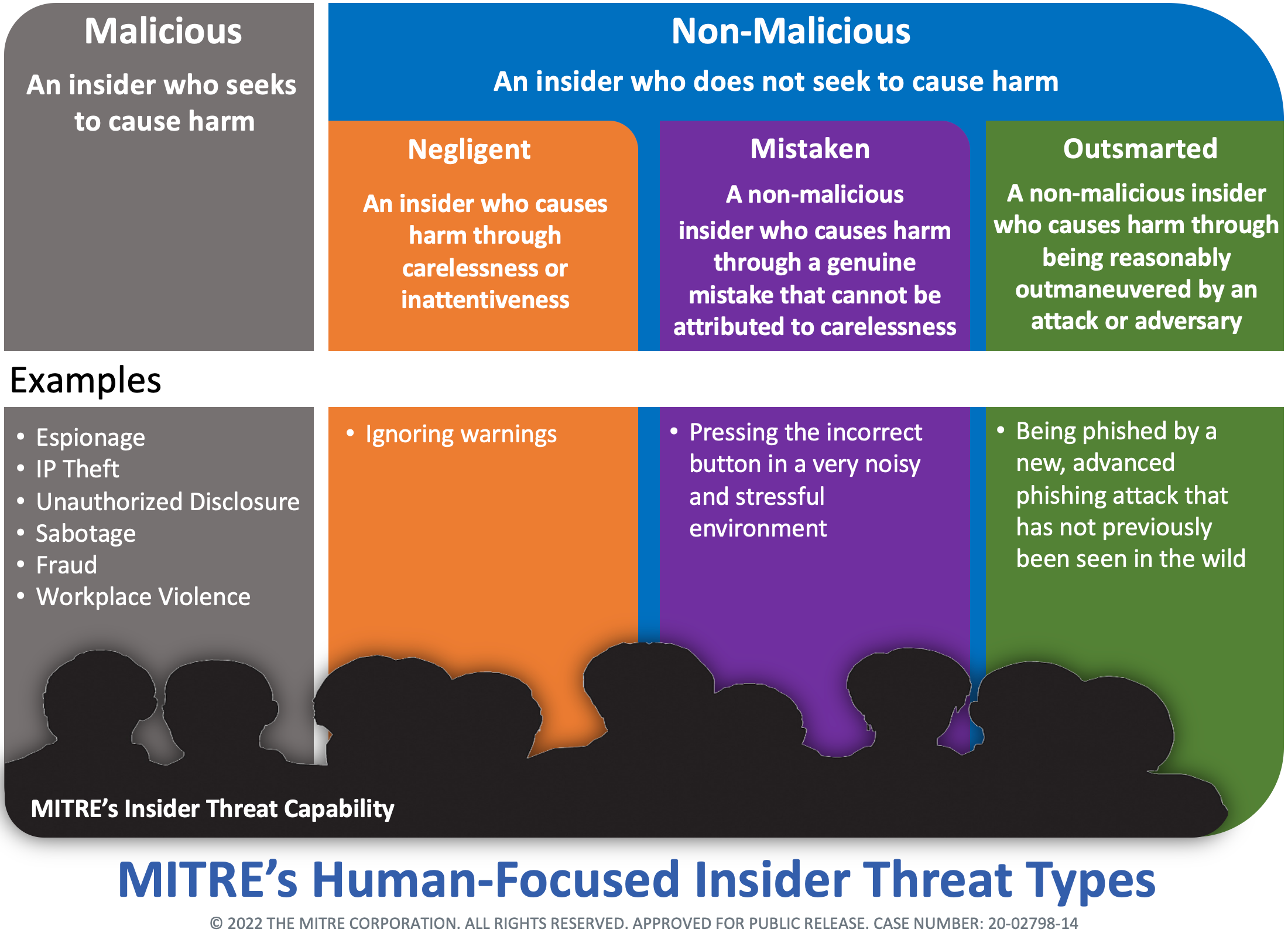
The insider threat community often distinguishes between malicious insiders (e.g., IP theft and sabotage) and non-malicious insiders. However, non-malicious insiders are generally oversimplified as employees who are negligent, which implies intent and blame, this can increase risk when employees who are negligent are treated as such during mitigations. MITRE’s behavioral scientists have generated and recommend a human-focused definition of non-malicious insiders to help the community think about and respond differently to employees. The diagram above distinguishes between three different types of non-malicious insiders: negligent insiders, mistaken insiders, and outsmarted insiders.
There are “negligent insiders”, namely employees within an organization who are negligent or careless. These employees create risk or cause harm taking actions where they do know and do not care. However, there are also “mistaken insiders”, namely employees who make genuine mistakes. For most employees, security is not their full-time job. They must already track and complete a multitude of tasks in their day-to-day work. Under those circumstances, particularly when employees are being asked to do more and more but with fewer resources, it is understandable that humans will make genuine but understandable mistakes that unintentionally create risks and could cause harm. Like technology, humans do not perform perfectly each day. The third group are “outsmarted insiders”. Computers and technology have zero-day vulnerabilities which are brand new vulnerabilities that are created by or can be exploited by adversaries. Humans have zero-day vulnerabilities too. Adversaries will try out new approaches to influence employees, create risk, and cause harm before we can even train our employees to look out for them.
Making the distinction between negligent insiders, mistaken insiders, and outsmarted insiders is important. The types of security mitigations for negligent employees should differ from the security mitigations for mistaken employees and outsmarted employees. As the insider threat community has been using a one-size-fits all definition of insiders, MITRE has seen improper and ineffective mitigations. For example, if an organization has an incident involving an employee being genuinely mistaken or outsmarted by an adversary, then responding to that employee as if they are a negligent insider by sending them to remedial security re-training or reporting them to their supervisor can create even more risk because those employees are more likely to feel helpless and quit all security vigilance effort.